On several recent occasions, ‘phishing’ attacks have sent official-looking emails to employees requesting that they click a link to verify their security information in SSO. The link did not go to https://sso.tamus.edu, but rather to an exact duplicate of the SSO logon page that was a phishing website used to capture their logon information. After entering their UIN and password, the employees received an error message instead of the familiar SSO menu. Their SSO credentials had been compromised by the fake site.
If you think your SSO account credentials have been compromised, you should change your password on the Profile tab immediately. You may also report any unrecognized logon activity from the Log tab.
— Please take the time to read the information below to learn how to protect yourself from phishing attacks. —
Phishing attacks use email or malicious Web sites to solicit personal, often financial, information. Attackers may send email seemingly from a reputable credit card company or financial institution that requests account information, often suggesting that there is a problem. When users respond with the requested information, attackers can use it to gain access to the accounts.
How do you avoid being a victim?
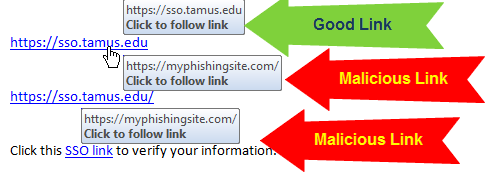
- In emails or websites, use your mouse to hover over a link to see where the link is actually pointed. In your email, it will be a small pop-up box like the image below. In your web browser, the link is usually displayed in the status bar or in a small pop-up box in the lower left of your browser window.
- Additionally from an email, you can copy the URL (on a PC, right click and “Copy Hyperlink”) and paste it into a browser window to see what the URL actually is before navigating to it.
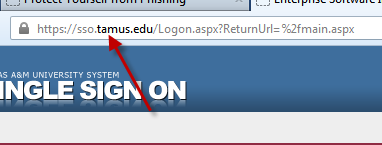
- Pay attention to the URL of a Web site. Malicious Web sites may look identical to a legitimate site, but the URL may use a variation in spelling or a different domain (e.g., .com vs. .net). When logging in to SSO, make sure the URL reads https://sso.tamus.edu.
- Be suspicious of unsolicited phone calls, visits, or email messages from individuals asking about employees or other internal information. If an unknown individual claims to be from a legitimate organization, try to verify his or her identity directly with the company.
- Do not provide personal information or information about your organization, including its structure or networks, unless you are certain of a person’s authority to have the information.
- Do not reveal personal or financial information in email, and do not respond to email solicitations for this information. This includes following links sent in email.
- Don’t send sensitive information over the Internet before checking a Web site’s security.
- If you are unsure whether an email request is legitimate, try to verify it by contacting the company directly. Do not use contact information provided on a Web site connected to the request; instead, check previous statements for contact information. Information about known phishing attacks is also available online from groups such as the Anti-Phishing Working Group.
- The US Government’s Cybersecurity & Infrastructure Security Agency provides helpful information about protecting yourself online and reporting a cyber issue.
- What does a phishing email look like? View an example of a message sent to actual A&M System employees like you.
What do you do if you think you are a victim?
- If you believe you might have revealed sensitive information about your organization, report it to the appropriate people within the organization, including network administrators. They can be alert for any suspicious or unusual activity.
- If you believe your financial accounts may be compromised, contact your financial institution immediately and close any accounts that may have been compromised. Watch for any unexplainable charges to your account.
- Consider reporting the attack to the police, and file a report with the Federal Trade Commission).
Provided by: Cybersecurity & Infrastructure Security Agency